by Reese Kimmons, MS ISA
It can seem as though tech people sometimes just make up new words and phrases or assign completely different meanings to existing ones.
That being the case, we believe it’s only right to give you some insight into what the techies are talking about.
We’re not just providing you with technology definitions here; we’ve also included helpful IT hints and advice.
So here’s your tech speak and IT jargon glossary laid out in simpler terms. We hope you find it useful.
Adware

Adware is software that gets downloaded to your devices as you browse the Internet. It displays ads on your screen, often without your permission.
Developers include adware in their code as a way of generating income. Adware is common in free software applications like the apps you download for your phone.
Adware can be dangerous. Get your phone and tablet apps from trusted sources like the App Store and Google Play.
Some adware can include spyware that will collect and transmit sensitive information about you and your online activities.
A good antivirus program set to update and scan for threats automatically can prevent the installation of spyware.
Android, Apple, and Blackberry operating systems
We’re not going to get too into the weeds here, but we did want to point out some significant differences between the operating systems used by Android and Apple, as well as give Blackberry die-hards some information they might need sooner rather than later.
Android OS

The operating system (OS) that is used by Android phones is based on a modified version of Linux and other open source code (see section on “open source” for more information).
It isn’t as secure as Apple’s iOS operating system used in iPhones, but it does offer Android users more flexibility to change configurations in their devices and to install applications from third-party developers.
This, however, means Android devices are more vulnerable to attack.
There is no standardized configuration for off-the-shelf Android devices. Manufacturers can vary the configurations of the phones and tablets they build.
The Android OS is also available on a wider variety of devices than the Apple iOS is. If you like having more control over what you can and can’t do with your device and what apps can be installed, Android is probably the right option for you.
Just be sure to get your apps from reputable sources like Google Play and run some quality antivirus software.
Apple iOS

iPhones run the iOS operating system, which is less customizable than Android. The devices are far more standardized than those running the Android OS.
More apps are available for Android devices in the Google Play Store than are available for iOS devices in Apple’s App Store, but you’re less likely to get malicious code from the App Store.
For these reasons, Apple devices are generally more secure than Android. For those who aren’t into installing third party apps that may pose a security risk or customizing their device configuration too much, an iPhone is probably the right choice.
Blackberry devices
Yes, there are still Blackberry devices out there, but they may not work for much longer. There are conflicting reports online. Blackberry devices were scheduled to stop working in January of 2021, but that has changed.
Many sources are now reporting that they will continue to be supported through the end of 2022.
Blackberry devices aren’t the most powerful or fastest devices out there, but some people just like the look and feel. So enjoy that mechanical keypad as long as you can, Blackberry fan. It may soon be a thing of the past.
Botnet

A botnet is a network of “zombie machines” infected by malware that allows a cybercriminal, or bot herder, to control them.
The owners of these machines usually have no idea that they are being manipulated remotely. The malicious activity typically happens behind the scenes, and the only evidence may be slowed performance.
Botnets are typically used to launch distributed denial of service (DDoS) attacks by flooding targeted network resources with so much traffic that they become unusable.
For example, a botnet may flood a router with requests, thereby making network resources inaccessible to users.
Cookies

When you visit websites, small text files called cookies are stored on your browser. First party cookies are those that collect information that allow the sites you visit to recognize your device when you visit them again.
These cookies allow for the collection and storage of details like login credentials for the site, information about what pages you have visited, what products you purchased, etc. They are relatively harmless unless a criminal gets access to them.
If, for example, a hacker is able to use credentials stored by a first party cookie, he may be able to access your account on that site or hijack an active session and impersonate you, perhaps allowing him to change your login credentials and steal things like stored payment card information.

Third party cookies are the ones you’ll want to avoid if possible.
These are also delivered by the sites you visit, but belong to entities other than the sites that deliver them. They follow you as you browse the Internet.
A third party cookie is like a stranger peering over your shoulder as you browse, taking notes about the sites you visit, the pages and products you view, the links you click, and more. They are used to build profiles on you based on your online habits.
Initially, third party cookies were used solely for gathering information for advertisers to allow them to target you with ads based on your browsing activities. Now, the information these cookies collect can be used for far more nefarious purposes.
Privacy-based browsers like Brave along with search engines like DuckDuckGo will block these third-party trackers.
Virtual private network apps (VPN) also prevent these little spies from tracking your activities by masking your device’s unique IP address. (See the section on VPNs.)
As a result of legislation enacted by EU members, websites that are accessible from those European nations are now required to provide notification to site visitors regarding their use of cookies.
This has become common practice world-wide, giving site visitors the option to decline cookies. Doing so can limit the usability of – and access to – the site.
There is a movement underway to eliminate the use of third-party cookies altogether due to privacy concerns. In fact, Google has announced that it will discontinue using them by the end of 2023. That’s a step in the right direction.
Dark Web

The Dark Web is the name given to the section of the Internet used by cybercriminals for nefarious purposes, including the exposure and sale of data stolen in breaches.
It is also used to recruit other criminals to form alliances in order to perpetrate attacks. Criminal organizations have begun to brazenly behave like legitimate businesses, recruiting others to assist them with their schemes.
Malicious software is also sold via the Dark Web.
The Dark Web resides on darknets. These are segments of the Internet that can only be accessed by those who have certain software applications, have special authorization, or use certain configurations.
They offer anonymity to their users, not requiring them to identify themselves or reveal their locations. This makes tracking the criminals more difficult for law enforcement officials.
Data brokers and people search sites

The combination of information collected by online trackers (cookies) and data available from other sources, including public real property records, legal filings, your Internet service provider (ISP), social media, and your Domain Name System service, can be combined to form what is often an alarmingly extensive personal profile.
If you’ve never done so, Google your name. The search results will include multiple “people search” sites. Take a look at a few of them.
The information they have collected will likely shock you. Data brokers and people search sites make this personal information about you and your family available to anyone willing to pay for it. This includes identity thieves and other cybercriminals.
Deleting data on people search sites
You can do something about this, but it’ll require some time and effort. You can visit each of the people search sites and go through their processes to remove your data and prevent them from collecting it in the future.
Fox News published a good article that will get you started. Bear in mind that this is an ongoing process. New people search sites are constantly coming online.
Another option would be to pay for a service like OneRep or DeleteMe to remove and keep your information out of these sites.
Other ways to minimize your online profile include using a privacy-based browser like Brave and its default search engine DuckDuckGo, using a virtual private network app to mask your identity and location, and switching over to a private DNS service like Quad9.
Domain Name System (DNS)

The Domain Name System (DNS) is the service that allows you to type in the names of websites rather than having to remember and enter their numeric addresses, which sometimes change.
Some DNS services keep logs of all of the sites you visit. Your Internet service provider (ISP) will typically assign a default DNS to you when you sign up for service.
Not long ago, it was discovered that major ISPs in the U.S. were gathering data from their default DNS providers and using it to track their customers.
You can change what DNS you use and select one like Quad9 that doesn’t track and record your activities. Many of these services are free.
All you need to do to use them is to make a small change in your device’s network settings. Privacy-based DNS service providers will give you the information you need to make that change.
DoS and DDoS attacks
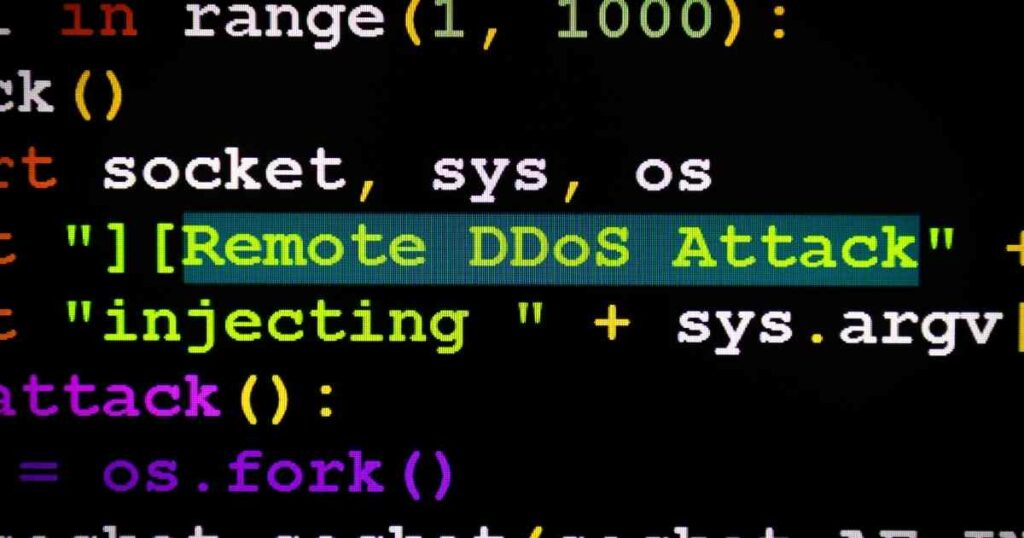
These abbreviations stand for Denial of Service and Distributed Denial of Service. In a DoS attack, the cybercriminal attempts to make a network resource unavailable to its users, usually by flooding it with traffic to overload it.
The same is true for DDoS attacks, but DDoS attacks flood the resource with traffic using a network of machines called a botnet, or zombie network.
DoS and DDoS attacks typically target routers to disrupt service on entire networks or servers to deny access to data. Imagine being in your office and being unable to log into any company resources, or even to get on the company network at all.
Email header
The header of an email is a snippet of code that includes information you can use to determine whether a message is malicious and whether the From address is the actual address of the sender.
You’ll need to know how to view the information in the header in your particular email app. To view pertinent parts of the header of a Gmail message, for example, you would simply click the down arrow in the To field. This will show you the underlying address of the sender.
If it differs from the address displayed in the From field, be careful. It may be some jumbled up bunch of characters, which often indicates the email came from a scammer. If you’d like to view all of the underlying code in the header and the rest of a Gmail message, click the three dots next to the reply arrow and select “Show original.”
If you use an email application other than Gmail, you can learn how to view a header in your email app by searching “how to view header in <your app’s name> email.”
Encryption

When you encrypt, or encode, data being transmitted or received by your phone, tablet, or computer using a virtual private network (VPN) app, you encode it so that it cannot be read by a cyber criminal.
A decryption key available only to the intended recipient automatically un-encrypts the data when it reaches its intended destination.
Stored data, known to techies as “data at rest,” is often encrypted by applications installed on the systems where it is kept so that, should a hacker gain access, that data will also be unreadable.
Some consumer grade backup drives have encryption capabilities that allow you to back up your important information and prevent it from being read by those not authorized to do so.
Endpoint attack

On a network, an endpoint is a user device. This can be a computer, smartphone, or a fixed-function device like a network printer. An endpoint attack targets an endpoint device, usually with the intent of using it to gain access to network servers and data storage systems.
Attackers can then do things like install ransomware (see the ransomware section for more information). That’s why it’s important to make sure that endpoint devices are secure, that their operating systems are kept updated to ensure that security patches get installed, and that, where applicable, they are running antivirus/anti-malware protection.
This is true whether the device is attached to your home network or your work environment.
“Eyes” alliances
Certain nations have formed “eyes” alliances that are surveilling the online activities of their citizens and others. For those of us concerned about the erosion of personal privacy, this is worrisome to say the least. The alliances are as follows:
- The 5 Eyes — The US, the UK, Canada, Australia, and New Zealand
- The 9 Eyes — The 5 Eyes + France, Denmark, Norway, and Holland
- The 14 Eyes — The 9 Eyes + Belgium, Italy, Germany, Spain, and Sweden
There are four additional nations that are believed to be providing assistance to the eyes members. They are Japan, Israel, Singapore, and South Korea.
The secretive activities of these alliances were well-hidden until 2003. A decade later, Edward Snowden leaked top-secret NSA documents revealing that these eyes alliances were not just spying on other nations that they considered security risks, but were also collecting information about their own citizens’ online activities.
If you’d like to know more, we’ve published an extensive article providing background on the eyes alliances. The article is written with a focus on selecting the right VPN to protect yourself and your information. You’ll find the article here.
Firewall

A firewall can either be a software application (like the one you probably have built into your home computer) or a hardware device. Firewalls are security tools that protect your computer or other resources on a network based on a set of rules that can be changed or added to as needed.
Firewalls monitor attempts to access your computer or other resources, and, based on the rules created, will block unwanted traffic and incoming communications from unrecognized or blocked sources.
If your home computer is running Windows 10, you can take a look at your built-in firewall and the settings it uses to block potentially dangerous and unwanted traffic.
Simply type “firewall” into the search box in the lower left of your screen and hit enter when the menu appears with the Windows Firewall control panel option highlighted. Just be careful if you make changes, as the firewall should already be configured with the best security options enabled by default (unless someone changed them previously).
Gateway

A gateway device connects a network to another network or network segment. You may have heard the terms gateway and router used interchangeably. In the past, they were always two different devices.
A gateway connected networks while a router delivered data within the network. It has now become common for these two functions to be combined into a single device typically referred to as a router that is used by small businesses and private home networks to connect to the Internet.
Host

A host, or network host, is a computer, server, or other device on a network. Hosts communicate with one another, sending and receiving data.
Some hosts provide services to others. Some provide application hosting that allows those apps to be accessed and used by others. Every host has a unique Internet Protocol (IP) address that identities it to the other hosts on the network.
HTTP and HTTPS

You’ve seen these abbreviations at the beginning of website addresses. HTTP and HTTPS are network protocols that establish connections between browsers and network servers. These protocols are the foundation of all Internet communications.
HTTP stands for Hypertext Transfer Protocol. HTTPS is the secure version of HTTP, thus the “S.” HTTPS adds encryption to the services provided by HTTP. This encryption service secures the communications between your device and the network server.
If at all possible, you should avoid sites that do not utilize HTTPS. In many instances, malicious websites do not use this secure version of the protocol. One easy way to determine whether your connection is secure is to look for the padlock icon to the left of the site address in your browser.
Internet Protocol (IP) address

An IP address is a unique identifier assigned to each host (or device) on a network. It identifies the device. In IP version four, the version most commonly used, the address is a series of numbers separated by dots (i.e., 127.0.0.1). A host on a network cannot communicate with others without having an IP address.
Because IP addresses identify your devices, they can be used to track your online activities. They also provide information about your geographical location. The data collected is used by data brokers and people search sites to build extensive individual profiles that they then sell to anyone who wants them.
See the sections on cookies, virtual private networks, and data brokers and people search sites for more information about how to minimize data collection and attribution based on IP addresses.
Keylogger

A keylogger is a piece of malware that records everything you type into your computer keyboard and sends the information to a cybercriminal. This could include your banking login credentials or payment card information. It could lead to your accounts being breached, your money being stolen, and perhaps escalate to full-blown identity theft.
It is important that all of the phones, tablets, and computers you use to access the Internet be equipped with antivirus software set to update and scan automatically and regularly in order to detect and stop a keylogger from being installed and stealing your sensitive data.
Kill switch

You might think of a kill switch as something that’s used to shut down equipment in the event of an emergency. That’s similar to what the term refers to in an IT context, where kill switches are used to disable or shut down an application or device.
One example of the use of a kill switch would be to disconnect your device from the Internet if you lose your virtual private network (VPN) connection. Because a VPN masks your device’s IP address and your identity and encrypts your data, the loss of a VPN connection could potentially expose sensitive information to a cybercriminal.
A kill switch would automatically disconnect your device from the Internet should your VPN connection be lost, thereby ensuring that your data is protected.
Latency
Latency is the amount of time it takes data to travel from one host to another on a network. It is an umbrella term that refers to multiple types of network communication delays.
Too much latency can manifest itself in poor website performance and delays in connecting with network hosts. Things like the physical distance between hosts and too many devices on a network segment can cause latency.
Malware

Malware is a broad term that is short for malicious software. Applications that steal data and/or damage or prevent devices from operating are malware. Malware includes viruses, worms, Trojans, spyware, keyloggers, and ransomware.
Visiting malicious websites or opening infected email attachments are a couple of ways by which malware can be installed on your devices.
You should be running antivirus/anti-malware applications on all of your phones, tablets, and computers that access the Internet. This software should be set to update, scan for, and mitigate threats automatically.
Multi-factor authentication

Multi-factor authentication (MFA), also referred to as two-factor authentication (2FA), adds another component to a login process.
Typically, when logging into an account that utilizes MFA, you’ll enter your username and password, then you’ll be prompted to enter a PIN number that is sent to your phone in order to complete the login process.
If a hacker manages to steal your username and password, he or she will still be unable to log into your account without having access to your phone and the PIN.
It’s a good idea to take advantage of MFA wherever it’s offered, especially if it is in connection with a financial or banking account.
Multi-hop VPN connection

If you’re not familiar with virtual private networks (VPNs), you may want to check out that section first. It’ll give you a better understanding of the information provided here.
A multi-hop VPN connection adds another layer of privacy on top of that already provided by standard VPNs. It does so by cascading, or chaining, multiple VPN servers together.
When you’re using a standard VPN that connects you to a single VPN server, a cybercriminal can see the IP address assigned by that server. It appears as the IP address of your device. In most cases, this provides sufficient security and will throw off attackers and online trackers.
But, if the cybercriminal can somehow break into the VPN server that assigned the IP address your device is using, he may be able to correlate the IP address assigned to you with the actual IP address of your device. This will allow him to identify you and track your activities despite your use of a VPN.
Chaining multiple VPN servers together in a multi-hop configuration makes it virtually impossible for attackers to accomplish this.
Open source

Open source software is software that can be modified and shared by developers because the code is publicly available and accessible. Collaborative participation is encouraged and celebrated in the open source community, as is transparency when it comes to the code behind the applications. When a vulnerability is identified, open source developers typically address it promptly.
Linux is an open source operating system used by many servers. The operating system used by Android devices is also based on the Linux open source code.
Open source code has been used to create many free applications available to anyone who wants them. One example is LibreOffice, a free and very good replacement for Microsoft Office that is supported and maintained by the open source developer community.
Packet (or data packet)

When data is transmitted across a network, it is divided into small packets. The TCP/IP protocol (see also sections on protocols and TCP/IP) does the dividing and packaging, preparing the data for transmission.
Once the packets reach their destination, the TCP/IP protocol reassembles them. If, for example, you’re sending an email with an image attached, it will be divided into small packets of information to make the trip.
Why is this done? Well, among other advantages offered by dividing data into packets, it provides error-correcting capabilities and allows for data to be transmitted over multiple pathways to expedite delivery of large files.
Phishing

Phishing is a word coined by techies to describe a social engineering attack wherein the perpetrator contacts the potential victim via email to try and persuade them to provide sensitive information or perform some other action that will benefit the attacker.
Ping
Sometimes we techies should give a bit more thought to the names we choose for things. For example, the word “groper” certainly has a negative connotation in most instances. But, when we use it as a part of the descriptive name “Packet Internet Groper,” or PING for short, it’s not quite so bad.
Ping is a software utility that acts as a way of determining whether a host is online and reachable. It also provides information about the time required for data to travel between that host and the device issuing the ping, also known as latency. Techies often ping devices and websites to check their availability and response times.
Protocol

Protocols are also known as access methods. Protocols are standards that define the ways in which data can be exchanged on every type of network from the Internet to the one in your home. They set requirements for things like how data is formatted, what to do with received data, and how to check for errors in data.
Perhaps the best known protocol is the transmission control/Internet protocol, or TCP/IP, which establishes communications standards for every computer connected to the Internet.
Ransomware

Ransomware is malicious software designed to block access to an organization’s sensitive and/or critical data, usually by encrypting it. It can be delivered and installed in many ways.
Very often, it’s installed as a result of a successful social engineering attack that takes advantage of an employee who lacks sufficient training to recognize the threat.
Once the ransomware is installed and does its job, attackers will demand a ransom payment in return for restoring access to the data. In many instances, however, access is never fully restored even if the ransom is paid.
Ransomware attacks can be so costly that some businesses don’t survive. In addition to the loss of access to their data, their reputations can be severely and irreparably damaged. Their customers lose trust in their ability to protect their information.
In a significant percentage of these attacks, victims who pay the ransoms are subsequently targeted multiple times because they have established their willingness to pay up. In other cases, extortion attacks follow wherein criminals threaten to expose the compromised data on the Dark Web if an additional fee is not paid.
Ransomware attackers are now targeting individuals as well as companies.
Region locking
Regional lockouts are used to manage access to websites, services, products, video, music, hardware devices and more by blocking access according to a user’s geographical region.
If, for example, you live in a country where the government doesn’t want its citizens to have the freedom to access certain social media sites, regional locking, or blocking, may be used to restrict that access.
This access management technique may also be used by providers of goods or services to protect their products from pirates, to avoid violating censorship laws in certain countries, to stagger the release of their products, or for other valid reasons.
Region locking is possible because IP addresses are assigned according to geographical regions. If, however, you are using a quality VPN application (see the section on virtual private networks), it is possible to defeat region locking controls.
A good VPN provider will have servers located in multiple locations world-wide. By connecting to, and receiving an IP address from, a server located in an unblocked region, users can bypass region locking controls. You should, however, take care if you do this, because in certain instances, your actions may violate applicable provisions of law.
Router
In the past, a router was a device used to route packets of data to their intended destinations within a network. Now, most people know a router as the device that connects their home networks to the Internet. That makes it both a router and a gateway device (see the section on gateways for more information).
Your home router is all that separates the devices on your home network from the threats that await them on the Internet. Routers provide your network’s perimeter security. If you’ve had your router for several years, it may be time for a replacement. Older devices may not be running the most current security protocols. See the section on WPA for more information.
There are things you can do with your router to better secure your home network. See the section on SSID for some tips.
Server

Servers are powerful computers that provide services to other network devices. These services may include file storage, hosting applications that are used by other network devices, or performing backups of other systems.
VPN services are hosted on servers, as are cloud computing resources. These are just some of the functions provided by servers. Some are even used to host multiple “virtual” servers that act as independent systems.
SMSishing
SMSishing is a word coined by techies that describes a social engineering attack wherein the scammer uses text, or SMS, messaging to convince a target to provide sensitive information or perform some action that will benefit the attacker.
Social engineering

Social engineering refers to the manipulation of targeted individuals to try and get them to divulge sensitive information or to take some action for fraudulent purposes. Scammers contact their targeted victims in person, by phone, via email, or through text messages.
They typically convey a sense of urgency and may even threaten their targets. They often impersonate someone in a position of authority and may, for example, even threaten a potential victim with arrest if they fail to immediately pay some non-existent fine.
Another example would be an attacker posing as a government representative threatening to cut off some form of benefits if the target fails to cooperate.
Scammers target organizations using social engineering tactics to do things like procure an employee’s login credentials. Attackers can then use those credentials to gain access to company systems, perhaps to install ransomware.
By conveying a sense of urgency, these criminals try not to allow their victims time to think about the situation or to verify the claims they make.
Split tunneling
Split tunneling is a feature of quality virtual private network (VPN) applications that allows you to use VPN encryption and other VPN functionality only where necessary, and routes the rest of your network or Internet traffic through an open network connection as you normally would.
An example would be if you are connecting remotely to your company’s internal resources via VPN, but still want to maintain “normal” connectivity when using other apps where no encryption is needed.
Split tunneling not only provides separate connectivity where you need it, but can also increase connection speeds (reduce latency) while you multitask.
Until recently, the average user most likely had no need for split tunneling. Now that many employers have transitioned to remote and hybrid work models, you might be working from home and split tunneling could come in handy.
Spoofing
Typically, spoofing refers to the act of concealing a real email address or phone number by replacing it with another. For example, if a scammer is targeting you, you might receive an email with a From address that indicates the message came from a company with which you do business.
But, if you expand the email’s header to reveal the underlying address of the sender, you’ll see that the address in the From field has been “spoofed.”
The same principle applies to phone calls and texts. You might get a text or call from a scammer displaying a number that looks a lot like yours (i.e., same area code and first three digits) when, in fact, that number has been spoofed.
Spoofing can also allow criminals to display a number that appears to be one belonging to your bank, making it more likely that you’ll fall for their stories and give them access to your account.
Spyware
Spyware applications secretly collect an organization’s or individual’s data by monitoring and reporting on their activities. This malware can be delivered and installed when you open a malicious email attachment or visit the wrong website.
In some instances, spyware can even take control over your device. To avoid it, only interact with secure sites (look for the small padlock next to the site’s address) and install a quality antivirus/anti-malware application on each of your devices used to access the Internet.
Set this software to update and scan for threats automatically so that any spyware or other malware that gets installed will be detected and removed.
SSID (Service Set Identifier)
Your Service Set Identifier, set by your router, acts as the name of your network. Routers and wireless access points (WAPs) broadcast the SSID to allow devices within range to connect.
If the network is secured, which your home network should be, credentials will be required to establish a connection. Hopefully, you’ve changed your router’s default credentials to something unique and complex.
It’s a good idea to change your original SSID because routers can be identified by the SSIDs they broadcast. Once a hacker has the default SSID, it can be very easy to determine the router’s make and model and to obtain the device’s default login credentials.
Hackers can also use the information to determine whether the router has any known vulnerabilities that could provide a way into your home network. If you have your router’s user manual, you should be able to find instructions for changing the SSID.
Changing your SSID
If you don’t have a manual, simply search online for instructions using the device make and model information that should be on a sticker affixed to the router.
When you change your SSID, don’t include any useful information like your name or address. You could have some fun with it and call it something like GetOffMe or FBISurveillanceVan. Get creative.
To add even more security to your home network, you can tell your router not to broadcast the SSID. When you need to connect another device, you’ll simply search for your network by its hidden name. You can find instructions for doing this the same way you found them for changing the SSID.
Torrenting
Torrenting refers to the downloading and uploading of Internet files via the BitTorrent network, a network of other users’ computers. This is also known as peer-to-peer (P2P) file sharing.
A group of these peers is called a swarm. To become a member of a swarm, you’ll need special software that allows you to connect to and use the BitTorrent network. The software is free and can be downloaded from multiple online sources.
Why would you do this? Using this P2P method, a peer can download large files in small pieces from multiple other users simultaneously, thereby lightening the load on centralized web servers and speeding up the download process. Uploading files works the same way. A peer can upload a file in small pieces to multiple peer machines.
Torrenting isn’t, in and of itself, illegal, but it is used by online criminals to unlawfully download protected materials like copyrighted movies, games, music, and software. You can get into trouble when using it if you inadvertently download things like this without authorization.
It may not be evident whether you are engaging in this unlawful activity, so you’ve got to be careful if you decide to give torrenting a try. Do some in-depth research first to keep yourself out of trouble.
Trojan

Remember the Trojan horse story? That’s where a Trojan virus gets its name. This malware is designed to look like a bona fide, trusted software application in order to trick you into installing it. When you do, the malicious payload is released to perform the hidden function for which the Trojan was created.
Trojans can be used to install software that spies on you and your online activities, takes control of your device, or steals your personal data, possibly leading to crimes including identity theft.
Be careful where you get the applications you install. Make sure they come from trusted sources. Avoid clicking on links in unsolicited emails or text messages to install applications. And as with other viruses and malware, make sure all of your phone, tablet, and computer devices that access the Internet are running quality antivirus applications.
URL – Uniform Resource Locator

A URL provides the location of a resource on the Internet. A website’s URL is made up of a communications protocol (see the HTTP, HTTPS section) followed by the name or address of a networked computer.
A website will have a primary URL that is often followed by additional addressing information that directs the browser to a specific page or file within the site.
Example of a URL: https://www.google.com/
Virtual private network

A quality virtual private network (VPN) application creates a secure tunnel between your device and the websites you visit. All traffic to and from your device is encrypted and protected by that secure tunnel.
If a hacker is somehow able to capture some of that data, he wouldn’t have the key required to un-encrypt and read it.
VPN benefits
While providing data encryption and secure connectivity are the primary functions of a VPN, it also offers other benefits. When you connect to a VPN, your device is given a new, temporary IP address to use for that connectivity session.
If you are using a good VPN, the server that assigns your temporary IP address will be one of many located around the world. Since different groups of IP addresses are assigned to different geographical locations, your actual physical location will be masked.
Another benefit of VPN usage is anonymity. Because a quality VPN app will utilize many VPN servers, each assigning different IP addresses to clients each time they connect, your online activities will essentially be untraceable.
Online trackers use your device’s IP address to compile information on you and your activities. When the VPN masks your actual IP address and assigns you a different one each time you use the app, it becomes impossible for those trackers to identify you and add details to your profile.
VPN types
There are four types of VPN – personal, remote access, mobile, and site-to-site.
Personal VPNs are just what the name implies. They are all-purpose VPN apps used by individuals to provide secure connectivity, anonymity, and location masking services while using their home computers and devices. They’re available for computers, phones, and tablets.
They aren’t expensive. In fact, some are even free. But free VPNs often lack sufficient infrastructure to support the traffic, sometimes resulting in unacceptable levels of latency and loss of connectivity.
We’ve done extensive work evaluating personal VPNs. Check out our reviews here. They will help you to find the personal VPN that best suits your needs.
Remote access VPNs are those provided by employers to be used by staffers working remotely. These VPNs ensure that company resources remain secure when being accessed from home offices or while employees travel.
Mobile VPN apps are also what the name implies. They can be used with mobile devices. Employers sometimes provide mobile VPN apps for remote employees to use when they don’t have access to dependable home Internet connections.
Site-to-site VPNs facilitate secure connections between multiple network locations or between companies that need secure access to shared data and systems.
Virus
In terms of computers and personal devices, viruses are segments of malicious code or programs written for the purpose of altering the way a device operates. These viruses, like those that affect humans, can spread from one device to another.
Viruses can be delivered in multiple ways, including via malicious websites and infected attachments to email messages. You should be using quality antivirus applications on all of your phone, tablet, and computer devices that connect to the Internet.
These applications should be set to update automatically and to scan for and mitigate virus threats periodically.
Vishing
Vishing is a word coined by techies to describe a social engineering attack wherein the scammer contacts the victim via phone to try and persuade them to provide sensitive information or take some other action that will benefit the attacker. The “V” in vishing stands for “voice.”
Vulnerability
A vulnerability is a weakness that can be exploited by a cybercriminal. Not every vulnerability is technical. If an employer fails to provide IT security training to its staff, the organization is vulnerable to social engineering attacks that target the human in the loop.
If you leave your house unlocked while you’re on vacation, your house is vulnerable to burglary. If you aren’t running malware protection or installing security patches on your devices, they are vulnerable to cyber attack.
Whistleblower
The meaning of whistleblower hasn’t changed. A whistleblower is someone who reports perceived wrongdoing. What has changed are the resources available to whistleblowers.
Now, if you believe you’ve observed wrongdoing, you can post your observations on social media sites for all the world to see. Government agencies have also published websites that whistleblowers can use to file official reports should they choose to do so.
Some agencies even offer rewards if the allegations prove to be factual. In some nations, laws have been enacted to protect whistleblowers from retaliation.
Worm
A computer worm is malware that replicates itself and spreads, or worms, its way into other devices across a network. Worms take advantage of vulnerabilities on network hosts in order to propagate by using the initial host machine to scan for other computers and infect them.
As with other forms of malware, having a quality antivirus/anti-malware application installed and set to scan for and remediate vulnerabilities will help you avoid worms.
Setting your devices to update automatically will also help you avoid a lot of infections. System updates often include security patches for recently discovered vulnerabilities.
WPA – Wireless Protected Access
WPA is a security protocol that secures your wireless (Wi-Fi) network. The Wi-Fi Alliance group has so far developed three security and certification levels for WPA: WPA, WPA2, and WPA3.
WPA was initially created to address security vulnerabilities in previous wireless security systems. WPA3 is obviously the newest version, but WPA2 is still in use. WPA, the first version, is considered outdated.
If your home router is running WEP (Wired Equivalent Privacy) or WPA rather than WPA2 or 3, it’s time for a new router. You may be able to find out which protocol your device is running by searching online using its make and model information.
Alternatively, you can find the version information by logging into your router’s interface and checking the system details. If your router was provided by your Internet service provider (ISP), you could check with them and find out whether replacement is warranted.
IT Jargon: In Closing…
Technical jargon is constantly changing due to the ever-evolving technological landscape we find ourselves in these days. We hope this IT jargon glossary and guide has helped put into simpler terms the specialized language of the Internet today.
You can always bookmark it and use it as a cheat sheet when necessary.
About the Author:
Reese Kimmons is an experienced IT executive with an AAS in Applications Programming, a BS in IT Management and an MS in Information Security and Assurance. During his time in the IT industry, Reese has earned certifications in ethical hacking, forensics investigations, ISO/GIAC, and Cisco networking.
- How Secure is Your Car? Tips to Stop Car Key Fob Hacking - December 17, 2022
- Cybercriminals Raking in Millions with “Hi Mom” WhatsApp Scam - December 17, 2022
- EU Websites Charging Visitors to Reject Tracking Cookies: A Practice Expected to Spread - December 17, 2022





