by Reese Kimmons, MS ISA
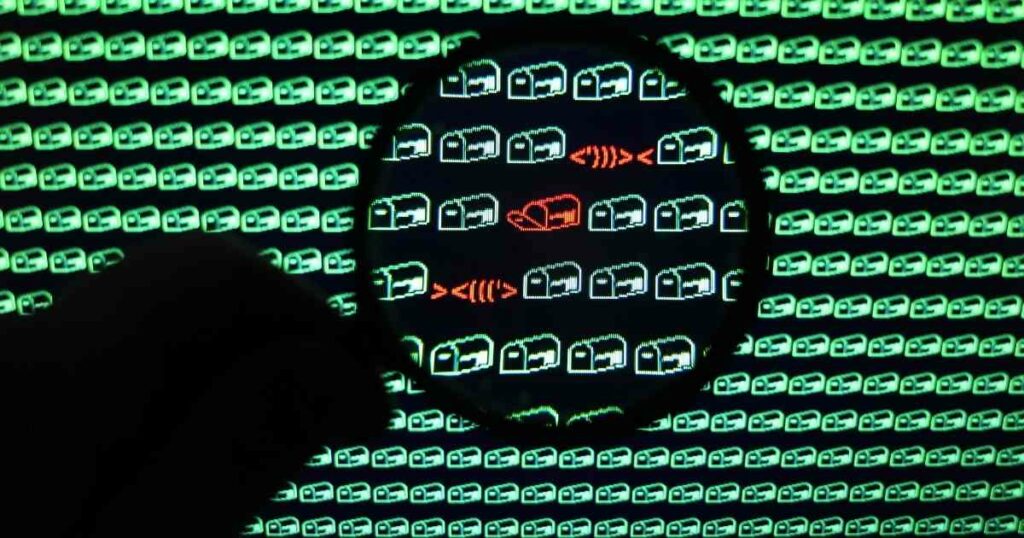
Company employees, often finance staff, are popular phishing email targets. A new phishing attack on the rise involves bad actors sending emails with “quarantine summaries” and lists of supposedly blocked messages to internal employees hoping to cause them to click on a link.
If they do, they will be taken to a malicious site designed to steal their email credentials – all for the purpose of financial gain for the threat actors.
Criminals have put some effort into making these phishing messages look legitimate, but employees can easily identify them if they know what to look for. If not, they may end up providing cybercriminals with access to critical resources.
How Spam List Phishing Scams Work

The recipient gets an email that, at first glance, looks as if it were generated by the company email server. The subject line may look something like this:
Quarantine summary: [ 9 message(s) quarantined from Fri 19 Nov 2021
The body of the email contains a list of quarantined message details divided into four columns labeled Date, From, Subject, and Web Actions. In the Web Actions column for each message are a red X and a green check mark.
The From and Subject details for each supposedly quarantined message listed do not relate to real emails and are simply concocted by the scammer.
These malicious emails include instructions advising the recipients to click the X next to a message to delete it from quarantine, to click the check mark to release it from quarantine and deliver it to the user’s inbox, or to click a third option that will delete all of the listed messages.
Clicking any of these options will have the same result. The recipient will be taken to a website where an email login form will be displayed. At the top of the login credentials box, a message indicates that the user’s session has expired and that they must sign into their email account again to continue the selected operation.
If they enter their login details and click the button to continue, their credentials will be sent to the bad actor.
Identifying this Phishing Activity
If these emails were legitimate messages, the sender’s address would indicate that it came from the organization’s email server. It would display the same domain information as that of the recipient’s email address.
Since sender names may be spoofed, recipients can hover their mouse pointers over the sender name to reveal the underlying email address. Alternatively, they can check the email header to find the sender’s actual address.
Different email applications require different steps to view headers, so users in your environment would need to be given the process that works with yours.
Another way to verify that these are phishing messages is to hover the mouse pointer over each of the buttons in the message body. Doing so will cause the underlying URL to appear.
With these messages, the URLs linked to all of the quarantined email delete-and-deliver options will be identical, because clicking any of them will take the recipient to the same fake email login page. The URLs will not be similar to those of internal company resources.
Once your users identify one of these malicious emails, whether they delete them, block the sender, report them, or all of the above will depend on whether you have procedures in place for them to follow.
In Closing…
Even the best email filters can’t block all malicious messages. Including this new type of phishing in your security awareness training and teaching your users how to identify malicious email messages and phishing techniques should minimize the chances that cybercriminals will be successful.
If you do not have one already, you may also want to consider adding a procedure or security strategy employees should follow if they receive suspicious emails.
About the Author:
Reese Kimmons is an experienced IT executive with an AAS in Applications Programming, a BS in IT Management and an MS in Information Security and Assurance. During his time in the IT industry, Reese has earned certifications in ethical hacking, forensics investigations, ISO/GIAC, and Cisco networking.
- How Secure is Your Car? Tips to Stop Car Key Fob Hacking - December 17, 2022
- Cybercriminals Raking in Millions with “Hi Mom” WhatsApp Scam - December 17, 2022
- EU Websites Charging Visitors to Reject Tracking Cookies: A Practice Expected to Spread - December 17, 2022


